Many teams work on software development projects: developers, testers, designers, and so on. Specialists have their own tasks, which they must complete by a certain date. How do you coordinate the actions of all teams? How to make sure that the design work goes according to plan and the product will achieve its goal? A product development roadmap helps to solve these issues. We will tell you why it is needed for a project.
What is a product roadmap?
A product roadmap is an important document, it is as necessary as Vision&Scope, SRS, Backlog and User Story Mapping.
A product development roadmap is a visual communication tool for a project team that is used when outsourcing project management services. This document describes the vision of the product and records the current working progress and long-term project goals.
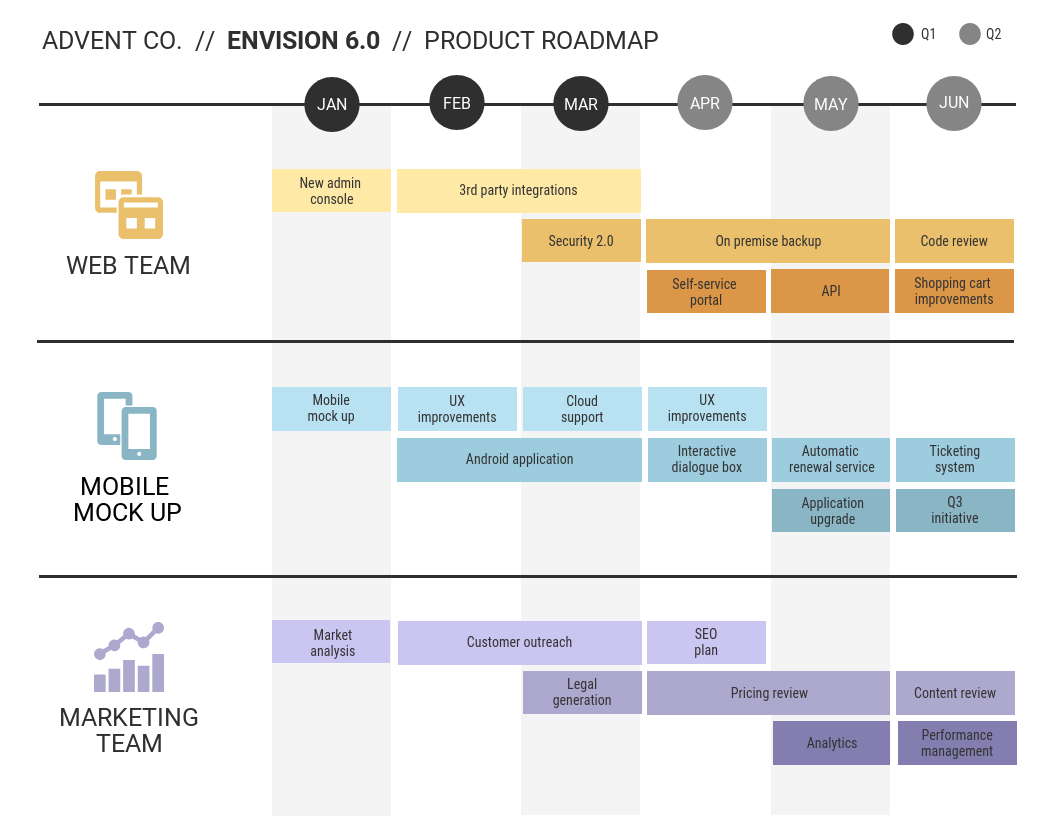
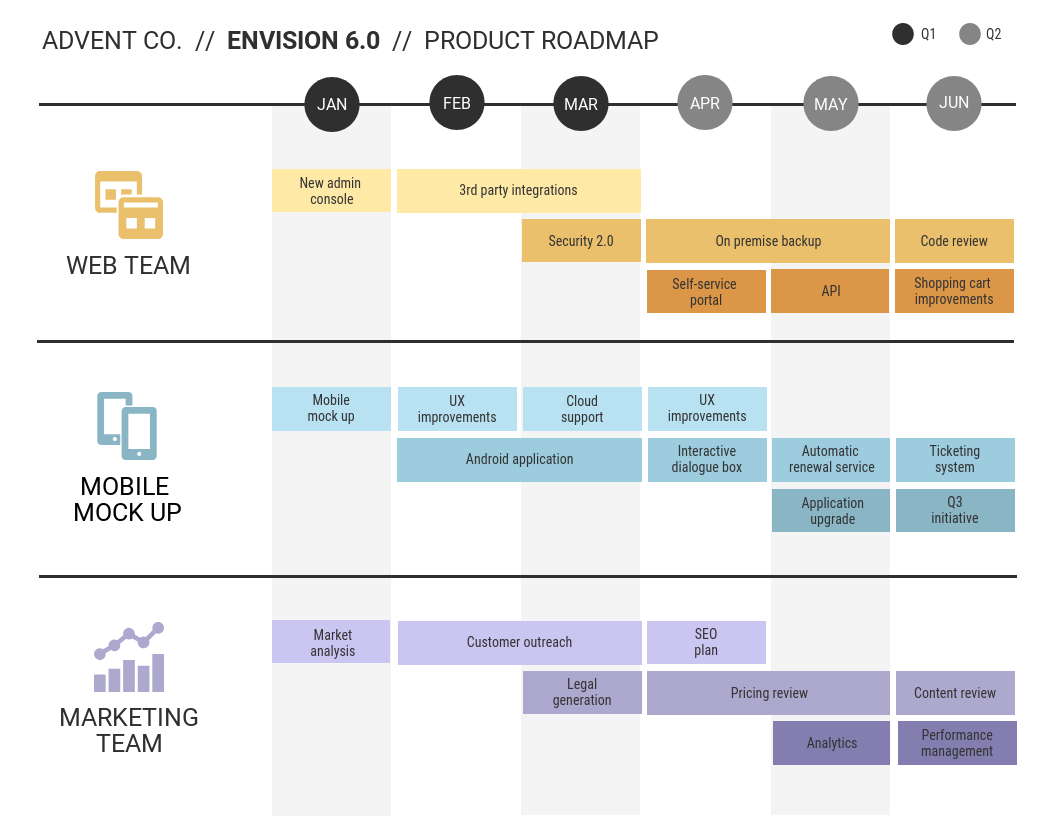
Source: venngage.com
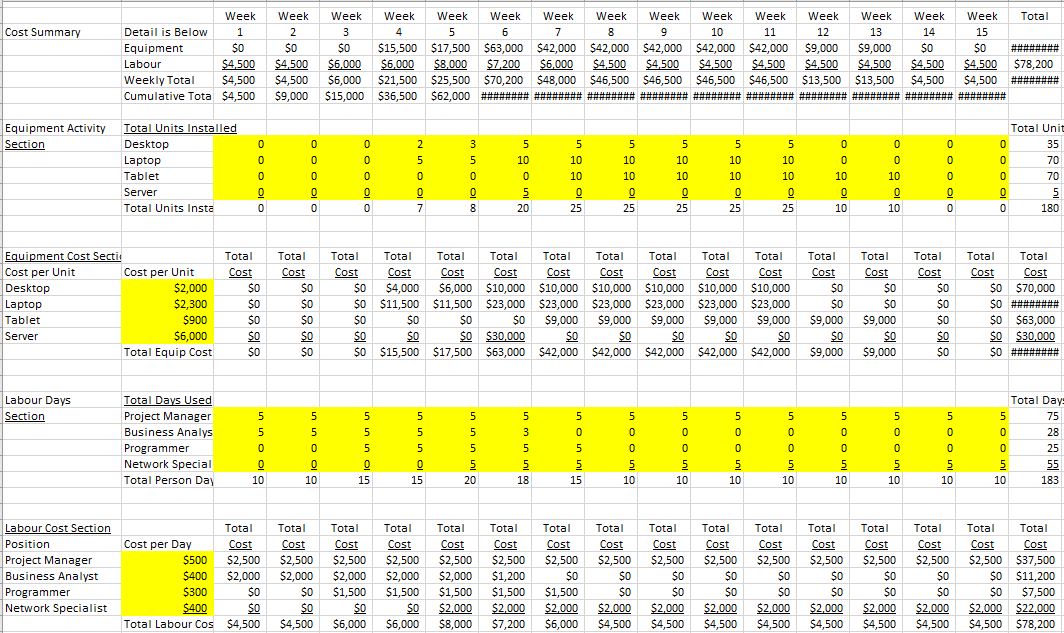
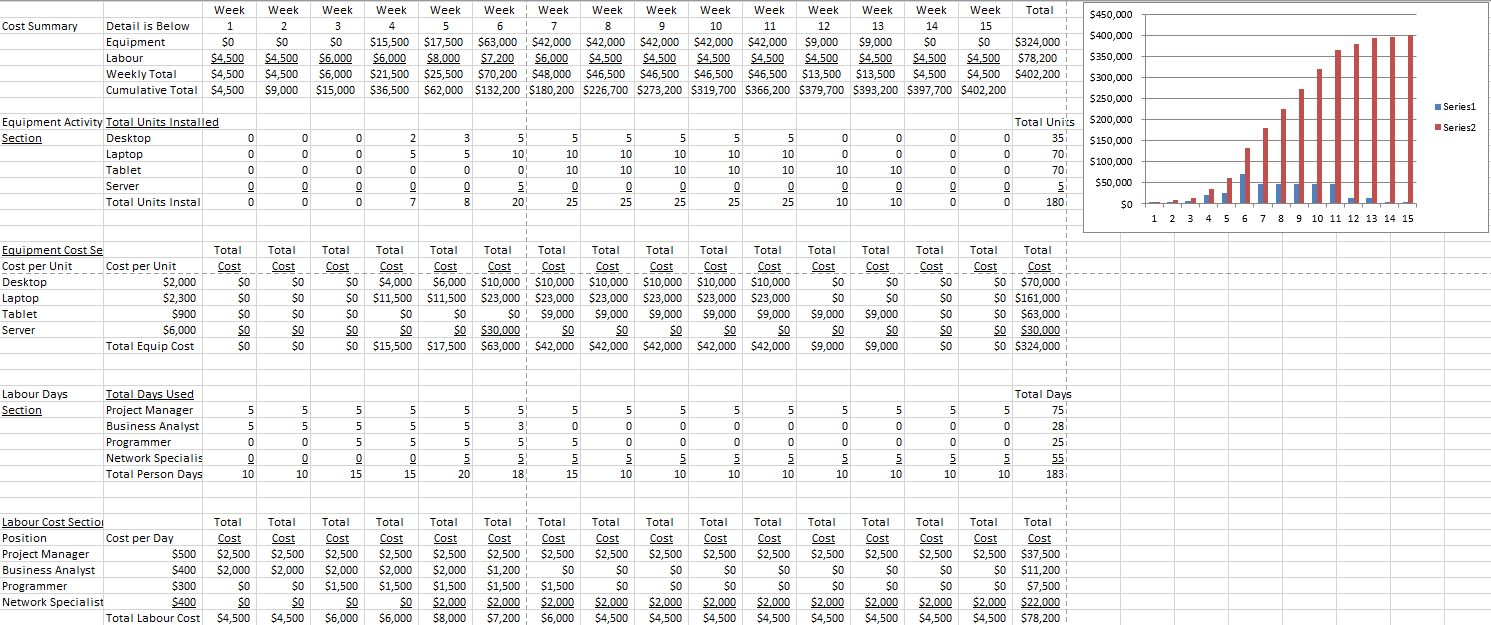
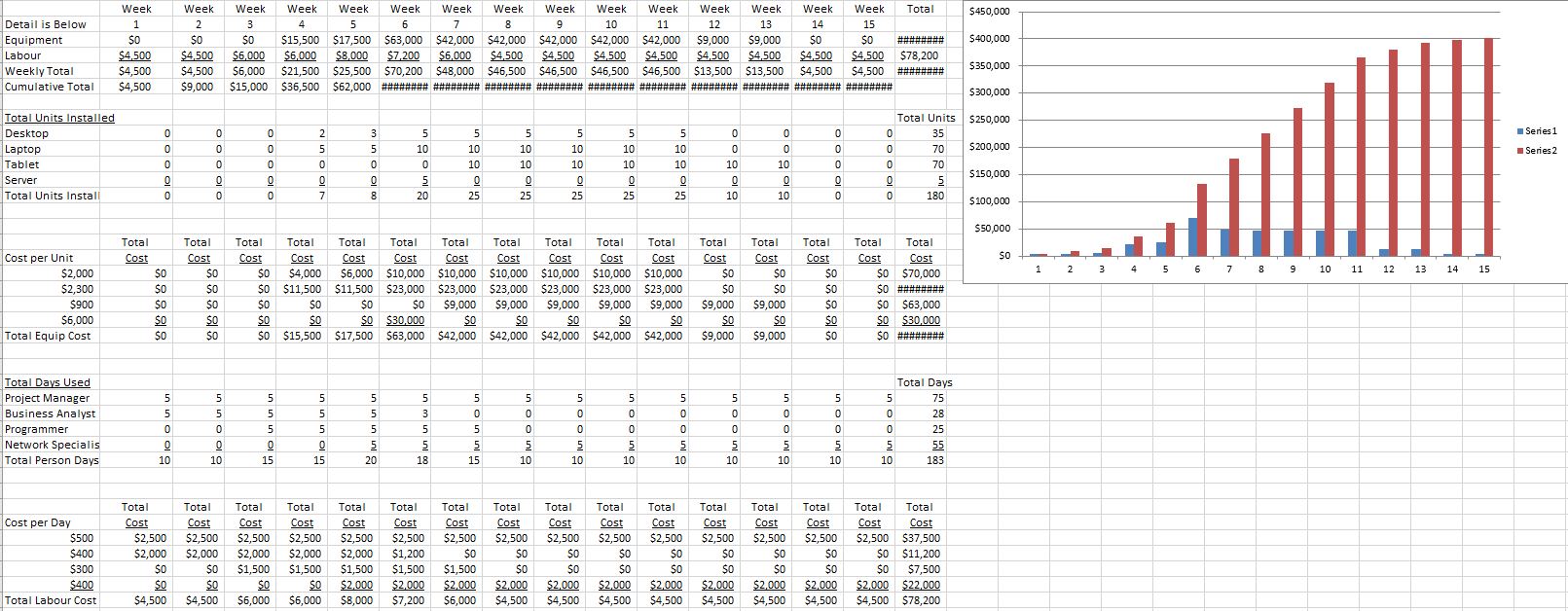
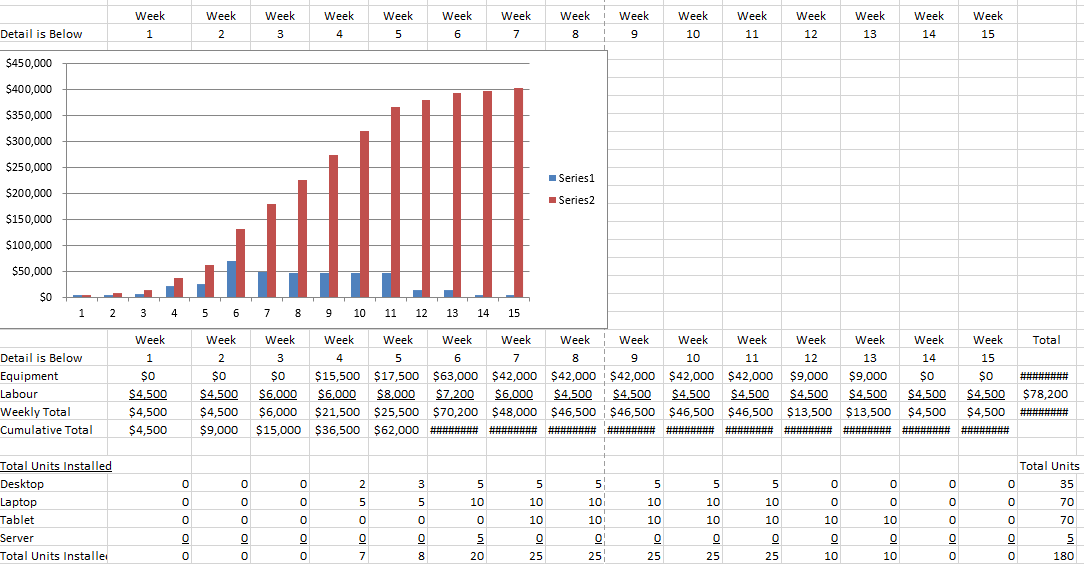
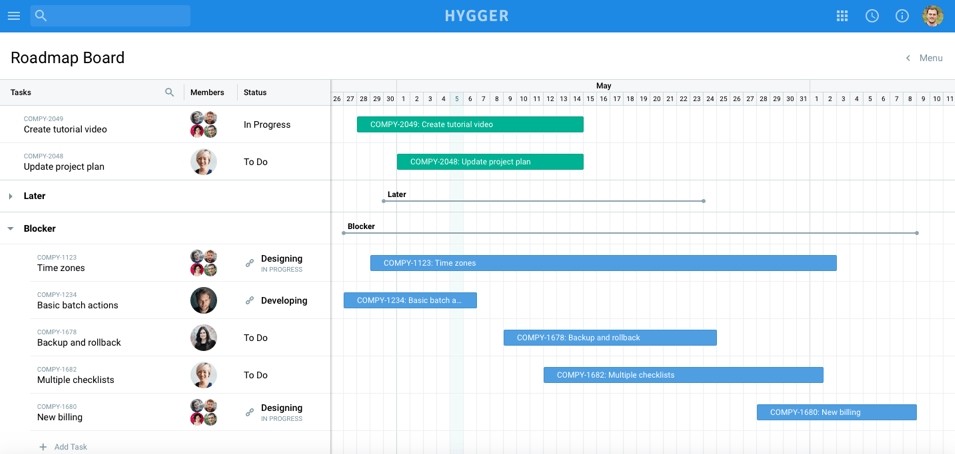
The main stages of work on the product are included in this plan, without dividing them into separate tasks. There, the names of performers and deadlines are indicated. Information is drawn up in tables, presentations or special programs. The picture must make it clear who is working on this or that task at a certain time.
The purpose of a roadmap is not to describe each project task but to give a visual representation of the global stages of work. It explains to the team why they need to implement certain functionality by a specified time. It illustrates what goals the product will achieve in the future. If specialists understand how the product will develop, it is easier for them to set up work on individual tasks.
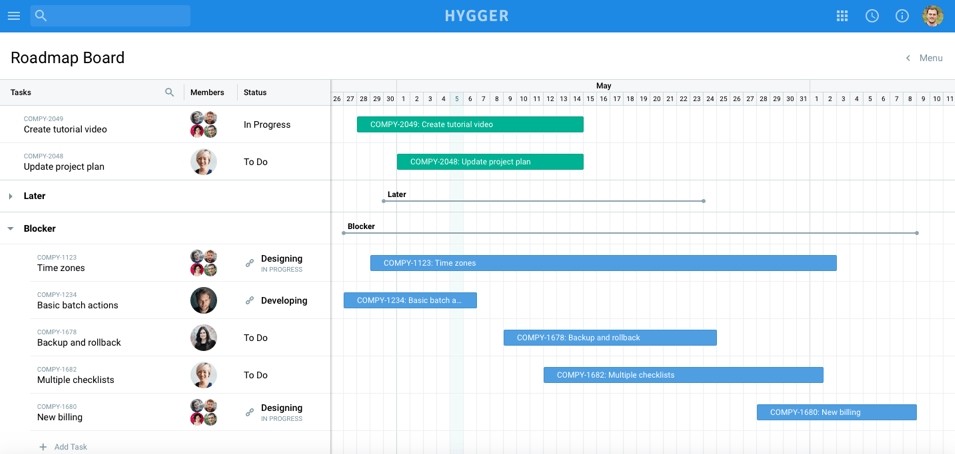
Source: habr.com
In other words, a roadmap is a product guideline for project teams, the marketing department, and customers. Project managers can change the roadmap when:
- the client modifies the requirements.
- it is necessary to enable a new feature at the request of users.
- there are internal problems.
- the market is changing.
The product development roadmap informs the project team and external interested parties (shareholders, customers, partners) about the main ideas and work progress.
Who needs a product development roadmap?
The product roadmap is used by internal development teams and external interested parties. Each professional benefits from this document and applies it differently:
The roadmap clearly illustrates to the project team how the product will develop. Engineers plan sprints and follow the progress of the project and the performance of the team. They see when additional specialists need to be involved in the project and rely on the document to bring the product to its final goal.
The marketing department relies on the product development roadmap when developing an advertising strategy and building a pricing policy.
The customer support department is using the product roadmap to answer user questions for future updates.
Project managers use a roadmap (product development roadmap) to report on the work done to the customers, investors, and partners. They see how the team is working on the product and how it will be developed in the future.
Advertisement
[widget id=”custom_html-68″]
Why a product roadmap is important for a project?
A roadmap helps project team members to understand the essence of a product. It also gives several benefits:
- It helps to define the product strategy.
Experts see what kind of work needs to be done right now and in the future. Project managers and customers see the full picture of what is happening on the project as part of the strategy.
- It is a good means of communication.
Usually, reviewing projects with each of the leaders takes hours of calls and discussions. The roadmap clarifies all the issues of software development. It is easy to create and update and takes less time to learn than during online discussion.
The map can be shared with everyone associated with the project (colleagues, management, and so on). With the help of this document, it is easier to convince investors of the prospects of the product and get funding.
- It helps to “navigate the terrain”.
When a team works on a new project, they face three obstacles:
- it is easy for them to “get lost” because they don’t know how to get to their destination.
- team members may be late because they don’t know how quickly they need to complete tasks.
- the team may run out of specialists when they are not aware of what work they have to cope with.
The product development roadmap addresses all these issues. Project participants see the current state of affairs and prospects. They know that this month they need to create an admin panel, and next month they need to do a third-party integration. They understand that a mobile version is being designed alongside the web application.
The roadmap proves that the custom software development company’s team is moving in the right direction at every stage of development.
How to create a product roadmap
For a separate project, a unique product roadmap is built. But there are general principles that should be considered when building. It is necessary to:
- Define the project strategy.
For a roadmap to be useful, the following issues need to be considered:
- It is important to focus on the results of product development. Detailed tasks with estimation are not included in the map. They will simply confuse the workers of project management outsourcing companies, external departments, and investors. This information is recorded in other documents.
- You should create a document for all project participants. Each specialist (manager, marketer, or customer support employee) looks at the roadmap differently. Some are interested in business goals, others focus on product areas, prioritization and timing, and so on. So as not to create a separate roadmap for different departments, it is worth considering one that will be useful for everybody.
- You should communicate the vision of the product. The map illustrates the history of product development. The team members see this and take steps in the same direction.
- The product roadmap must be regularly updated. Changes often occur in projects: the customer changes requirements, asks to implement a new function, and so on. These changes must be included in the product roadmap, otherwise, it will become useless, and the team will go astray.
- Gather product requirements.
To determine the stages of work on the product, you need to know what functionality needs to be created. To do this, a business analyst collects product requirements, which are then documented (Vision & Scope, SRS, Backlog and User Story Mapping). This data can be used to point out top features, prioritize them, and build a product development roadmap.
- Select the roadmap format.
A product development roadmap can be drawn up in Excel, PowerPoint, or special tools. However, whichever program the project manager uses, they will choose one of the three traditional types of the roadmap:
- Product roadmap without dates. It is used on agile projects where priorities change quickly.
- Hybrid product roadmap. Such a map has approximate dates (by months) and stages of work sorted into current, upcoming, and future periods.
- Product roadmap with dates. Stages of work are planned with an accuracy of days in a month. This is especially convenient on projects where several departments are involved, and their tasks are related.
If the PM does not need strict deadlines, they choose the first and second options. Usually, this means planning works for a month or a quarter.
- Adapt the roadmap for all participants.
The product development roadmap is a guideline for internal and external teams:
- The management wants to see in it a product strategy and information about the current state of the market.
- Marketers are interested in seeing the product in comparison with competitors and its potential.
- The sales department is more concerned about the time of the release of the product and its competitive advantages.
- For developers and other IT professionals, requirements, deadlines, and sprints are more important.
Therefore, it is worth considering how to include this information in one document.
- Share the product roadmap.
The roadmap illustrates the team’s work progress and future goals. If the project manager shares the map with everyone, the participants will always be aware of the current state of the product and possible changes. Therefore, specialists will not spend hours clarifying the details of the project and other issues.
Customers value transparency in the work of their IT partners. Constant feedback, honesty and openness are big advantages for custom software development companies.
Which projects need a product roadmap?
Roadmaps can be used on traditional (Waterfall, Spiral) and flexible (Agile, Scrum) projects. This document focuses on the strategy of the product, not on the methods of its implementation.
For classic projects, a product development roadmap with dates will do. Flexible projects are limited to monthly and quarterly scheduling without clear dates.
The main difference is in the following:
- Waterfall projects are usually business-oriented and based on financial metrics. Agile teams are focused on customers and customer satisfaction.
- Waterfall roadmaps are usually scheduled for a year. An Agile map illustrates quarterly work.
- Waterfall teams communicate sequentially as new specialists join the project. Agile project participants work in a cross-functional environment and are simultaneously involved in the project.
- Roadmaps for Waterfall projects are more static. Maps for Agile projects are as flexible as the methodology itself.
Either way, both classic and agile teams will benefit from a product roadmap. They will be able to follow the strategy, meet deadlines and lead the product in the right direction.
Conclusion
A product development roadmap is created to make life easier for all project participants. It is a tool that developers, testers, designers, sales teams and businessmen are guided by. It ensures that the product develops according to plan and reaches the market on time. With a roadmap, the product is not a mere abstraction. It is a completely tangible solution with short-term and long-term goals and a visible result.